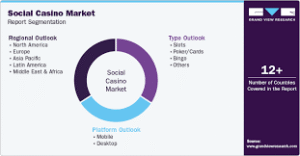
What Is Front Running in Crypto? How MEV Bots Extract Value From Your Trades


Front running is a practice with roots in traditional finance: a broker sees a large client order coming and places their own trade first, profiting from the price movement the client’s order will inevitably cause. On Wall Street, this is securities fraud. In crypto, it is automated, pervasive, and completely unregulated, and it is costing traders hundreds of millions of dollars per year.
The scale is not theoretical. HoudiniSwap has reported that sandwich attacks alone, one specific type of MEV front running, have extracted more than $900 million from DeFi traders. Total DeFi-related losses in Q1 2026 already exceeded the equivalent period in 2025, according to blockchain security tracking data. The bots running these strategies are not rogue actors. They are rational market participants exploiting a structural feature of how public blockchains process transactions.
Understanding how this works is the first step toward choosing a trading bot that actually protects you.
What the Mempool Reveals About Your Trade Before It Executes
Every transaction on a public blockchain like Ethereum or Solana passes through a waiting area before it is confirmed. On Ethereum, this is the mempool. On Solana, the pending transaction broadcast layer serves a similar purpose. These pools are, by design, publicly visible. Any participant with the right software can see what trades are pending, what tokens are being swapped, at what size, and at what slippage tolerance.
This transparency is a feature for network integrity and a vulnerability for anyone using a trading bot or sniper bot without built-in protection. MEV, which stands for Maximal Extractable Value, is the collective term for profit that can be extracted by controlling which transactions get included in a block and in what order. Block builders, validators, and specialized bots all participate in this market. The result is an adversarial environment where your pending trade, visible to thousands of monitoring bots, becomes an opportunity for someone else to profit before you do.
The mechanics operate faster than human perception. By the time you click confirm on a DEX swap, bots have already analyzed your transaction, calculated the profit opportunity, and submitted competing transactions designed to execute around yours.
How a Sandwich Attack Actually Works

The sandwich attack is the most common and most damaging form of front running in crypto. The mechanics are precise.
A bot monitors the mempool and detects your pending swap, buying a token on a decentralized exchange. It calculates exactly how much your purchase will move the price, based on pool liquidity and your trade size. The bot then submits two transactions. The first buys the same token just before your trade, driving the price up. Your trade executes at the now-higher price, within whatever slippage tolerance you set. The bot’s second transaction immediately sells the tokens it just bought at the price your trade pushed up. Your transaction is sandwiched between theirs, and you paid for the bot’s profit through worse execution.
This is not occasional. Solana’s high throughput and low fees make it especially attractive for sandwich bots because the cost of attempting an attack approaches zero, while success pays out on every victim. The crypto researcher known as pashov described a detailed account of this type of extraction on X (formerly Twitter) that accumulated 18,000 views and 246 likes, with traders recognizing their own experiences in the narrative.
The problem extends beyond individual losses. When enough value is systematically extracted, it degrades the economics of on-chain trading for everyone, widening effective spreads and reducing confidence in decentralized markets broadly.
Block Builders and the Transaction Ordering Economy
The architecture behind front running involves block builders. On Ethereum post-merge, block construction is largely outsourced to specialized entities through MEV-Boost, middleware that allows validators to accept blocks built by third parties. These builders compete to construct the most profitable blocks, which naturally includes maximizing MEV extraction opportunities.
The practical implication is significant: even if no individual bot successfully front runs your transaction, the block builder selecting which transactions to include and in what order can still capture value from your trade. This is sometimes called backrunning or transaction ordering manipulation. The public mempool is not a neutral waiting room. It is an open order book for extraction.
Jito, the dominant block production infrastructure on Solana, operates on a similar principle but with meaningful differences. Jito bundles allow transactions to be submitted as atomic groups, which provides genuine protection when used correctly, because a bundle that fails simulation gets dropped entirely rather than partially executing in a vulnerable position.
What Protection Mechanisms Actually Prevent Sandwich Attacks
Four approaches provide real protection, each with different tradeoffs.
Private mempool routing is the most complete solution for Ethereum. Instead of broadcasting your transaction to the public mempool where bots can see it, a private transaction goes directly to block builders through a protected channel. The transaction is invisible to front-running bots until it is already included in a block. By that point, there is nothing left to front run. This should be the default, not a setting you need to remember to activate.
Jito bundle infrastructure on Solana achieves a similar outcome through atomic transaction grouping. A bundle succeeds entirely or fails entirely, which removes the partial execution vulnerability that sandwich bots exploit. Correct Jito configuration also reduces the window during which your transaction is visible to adversarial nodes.
MEV-aware execution logic on chains like BNB Chain and Base involves routing intelligence that accounts for known extraction vectors when selecting execution paths. This is less absolute than private mempools but meaningfully reduces exposure on chains where private routing infrastructure is less mature.
Pre-flight simulation addresses a related but distinct threat. Before committing funds, a simulation run against live chain state can detect honeypot mechanics, hidden minting functions, and malicious contract logic that would cause your trade to fail or be exploited at the contract level rather than the mempool level. When simulation fails, the trade should be blocked automatically, not just flagged.
The critical distinction across all four approaches is whether protections are on by default or require the trader to find and activate them. A protection that users must opt into will, in practice, be missed by the traders who need it most.
How Platforms Are Building MEV Defense Into Default Execution
The better trading bot platforms have moved past treating MEV protection as a feature checkbox. Banana Gun applies MEV protection as the default execution layer across all five supported chains, with no opt-in required. On Ethereum, this means bypassing the public mempool entirely through private transaction routing. Sandwich bots cannot observe the transaction before it is confirmed in a block. On Solana, Jito infrastructure handles bundle-level protection. On MegaETH, the routing engine was rebuilt specifically for the chain’s 100,000 transactions-per-second environment, where millisecond-level MEV resistance requires different architecture than slower chains demand.
Banana Pro, the platform’s browser-based crypto trading app, adds pre-flight simulation through the Banana Simulator. Every transaction is tested against live chain state before any funds are committed. If the simulation detects a honeypot, a hidden minting function, or contract logic designed to trap funds, the trade is blocked automatically. This runs across all five supported chains: Ethereum, Solana, BNB Chain, Base, and MegaETH.
Beyond sandwich attack prevention, this trading bot runs real-time contract monitoring after purchase. A synced Telegram trading bot provides the same protection layer on mobile. This addresses rug pulls directly, where developers withdraw liquidity or modify token tax parameters after traders have already entered a position. The system monitors for sudden liquidity withdrawals, tax structure modifications, and developer blacklisting actions, reporting an 80 to 85 percent success rate at detecting and fronting the rug transaction before it completes. A Transfer on Blacklist feature redirects tokens if a developer blacklists a user’s address, and Reorg Protection guards against block reorganization attacks on all chains.
Traders executing token entries during high-MEV launch windows face compounded risk: mempool exposure at the moment of maximum bot attention. The platform’s guide on what MEV actually costs traders on every DeFi transaction covers this scenario in depth. Having private mempool routing and simulation active by default, rather than as an afterthought, is what separates a protected entry from an expensive lesson.
The platform has processed $16 billion in cumulative trading volume across 25.3 million trades with this protection layer active. That volume base provides a real-world signal about performance in live market conditions, not just theoretical protection architecture.
What Traders Can Do Right Now
Not all protection requires switching platforms. Some practices reduce exposure on any interface.
Set tighter slippage tolerances where liquidity depth allows. A 15 percent slippage setting is an open invitation for sandwich bots; a 0.5 percent setting on a liquid pair removes the profit opportunity for most attacks. Verify token contracts on-chain before trading, not just through the DEX interface, since malicious contracts can spoof legitimate-looking token information. Trade during periods of lower mempool congestion, which reduces the window your transaction is exposed to monitoring bots.
For active on-chain trading, the more meaningful change is using infrastructure that applies private mempool routing by default. The public mempool is a transparent market for extraction, and every unprotected transaction passing through it is one that bots had the opportunity to analyze and act on before it confirmed. The bots are faster than any human trader, they run continuously, and they are optimized for exactly this activity. The asymmetry is structural.
Front running in crypto is not going away. The economic incentives for MEV extraction are built into how public blockchains process transactions, and the participants running these strategies adapt to any public countermeasure. The practical answer is not to wish the problem away but to stop broadcasting your trades to the bots in the first place.
Frequently Asked Questions
What is front running in crypto?
Front running in crypto occurs when a bot detects a pending transaction in the public mempool and submits its own transaction first, profiting at the original trader’s expense. Because blockchain transaction ordering is determined by fees, bots can pay higher fees to jump ahead in the queue. Unlike traditional markets where front running is a federal crime, crypto has no regulatory prohibition on this practice. The process is fully automated, operating at machine speed across thousands of pending transactions simultaneously.
What is a sandwich attack in crypto?
A sandwich attack is a specific form of front running where a bot places one transaction immediately before a victim’s trade and another immediately after it. The first transaction moves the price against the victim. The victim’s trade executes at that worse price. The bot’s second transaction sells at the inflated price, locking in a risk-free profit. HoudiniSwap has reported that sandwich attacks have extracted over $900 million from DeFi traders across the ecosystem.
How can you protect yourself from MEV bots?
The most effective protection against MEV bots is private mempool routing, which prevents bots from seeing your transaction before it is included in a block. On Ethereum, this means bypassing the public mempool entirely. On Solana, Jito bundle infrastructure provides comparable protection through atomic transaction grouping. Platforms that make MEV protection the default for all trades, rather than an optional setting, offer the most reliable defense in practice. Pre-flight transaction simulation adds a second layer by catching problematic contract mechanics before any funds are committed.